This how‑to guides you through enabling Multi‑Factor Authentication (MFA) in CoreView to secure your Active Directory and Microsoft 365 environments.
While passwords remain the most common method for verifying a user's identity, they are highly susceptible to cyberattacks such as phishing and password spraying. By enabling MFA, you add an extra layer of security that requires at least two verification methods, effectively blocking potential attackers from accessing your systems and helping to prevent serious financial and operational damage.
The process described below is not applicable to enabling MFA via a Conditional Access policy.
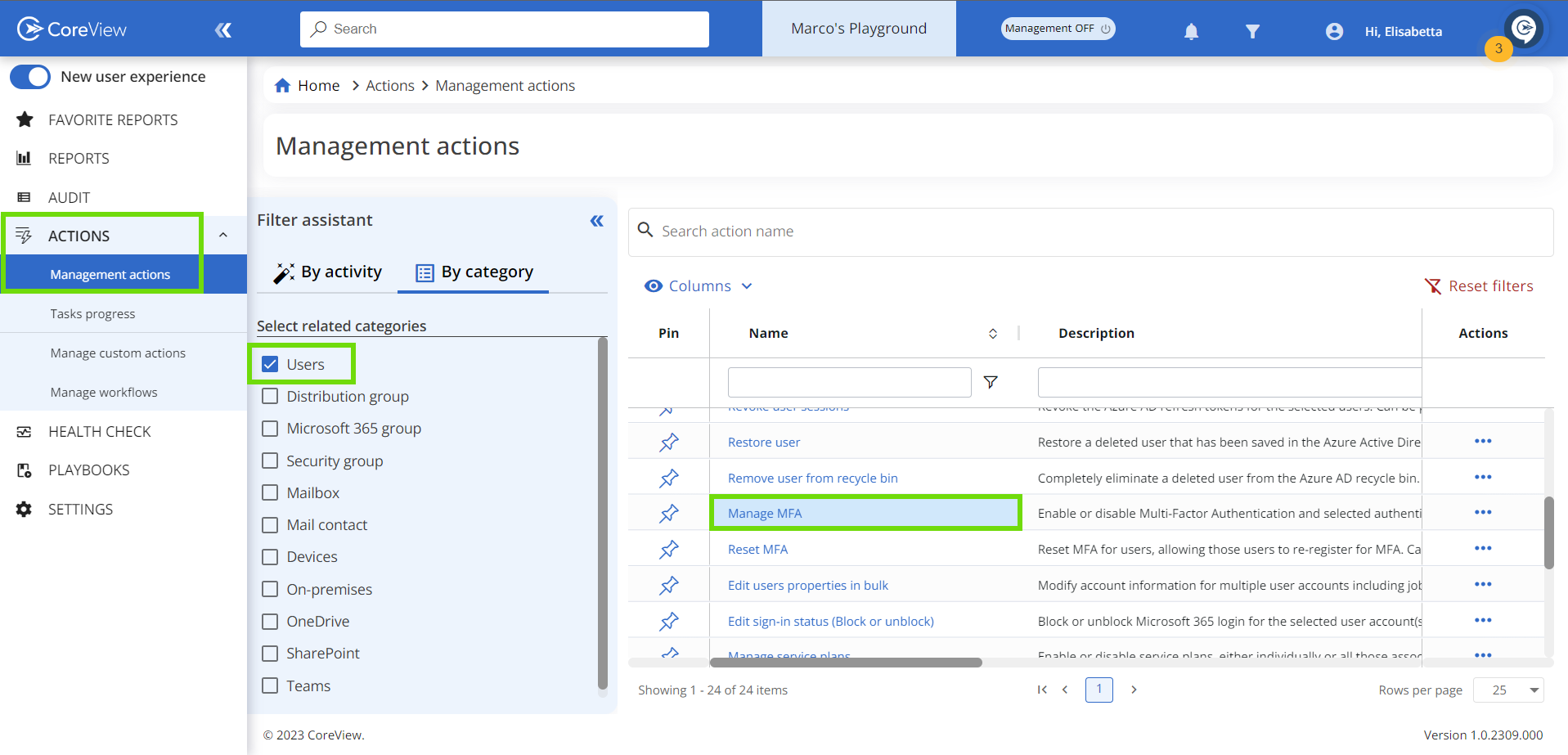
- Under “Actions > Management actions” select “User” and click on “Manage MFA”
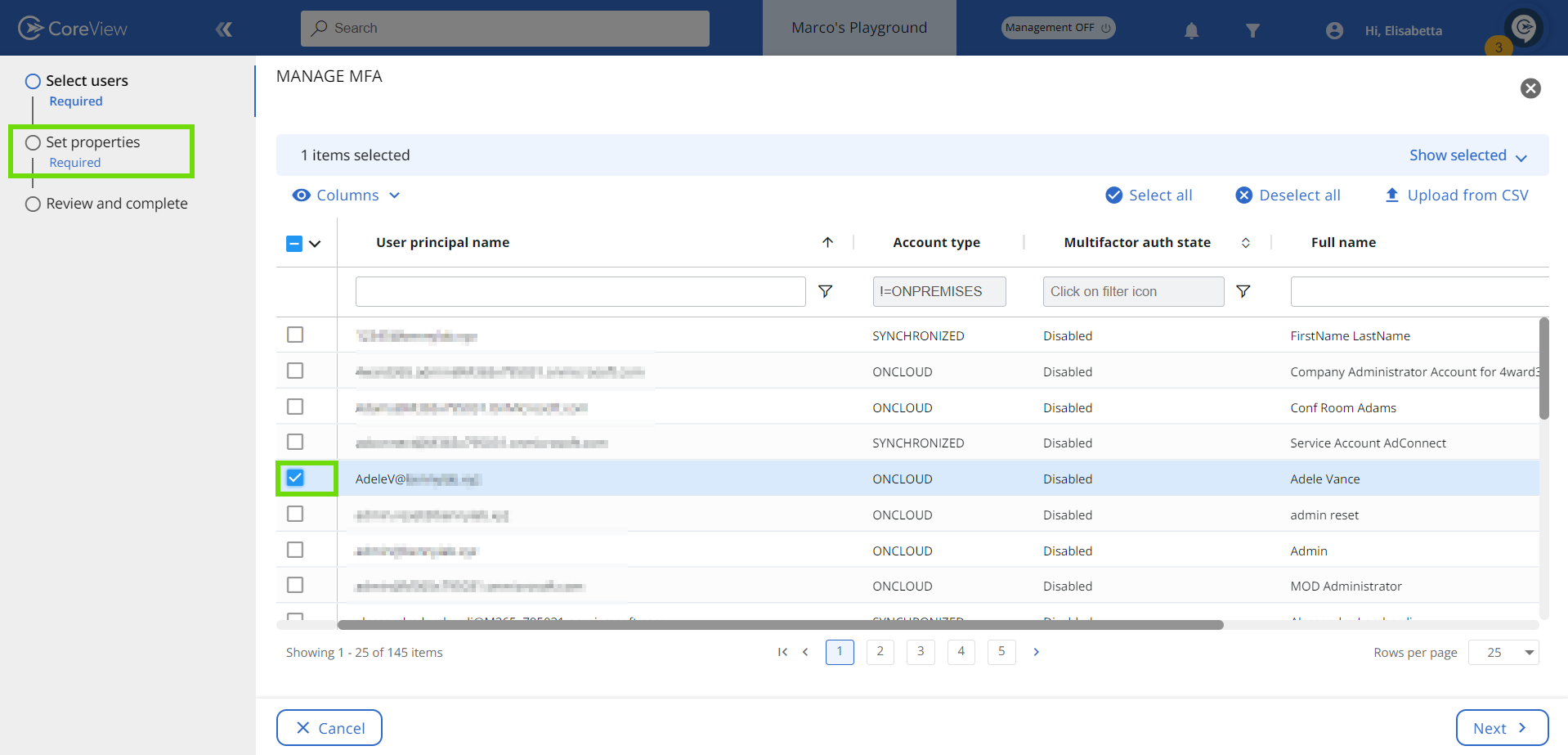
- On the next page select the user(s) for whom you want to enable MFA and click “Next”.
- Under “Authentication info” select “Enabled” from the drop-down menu.
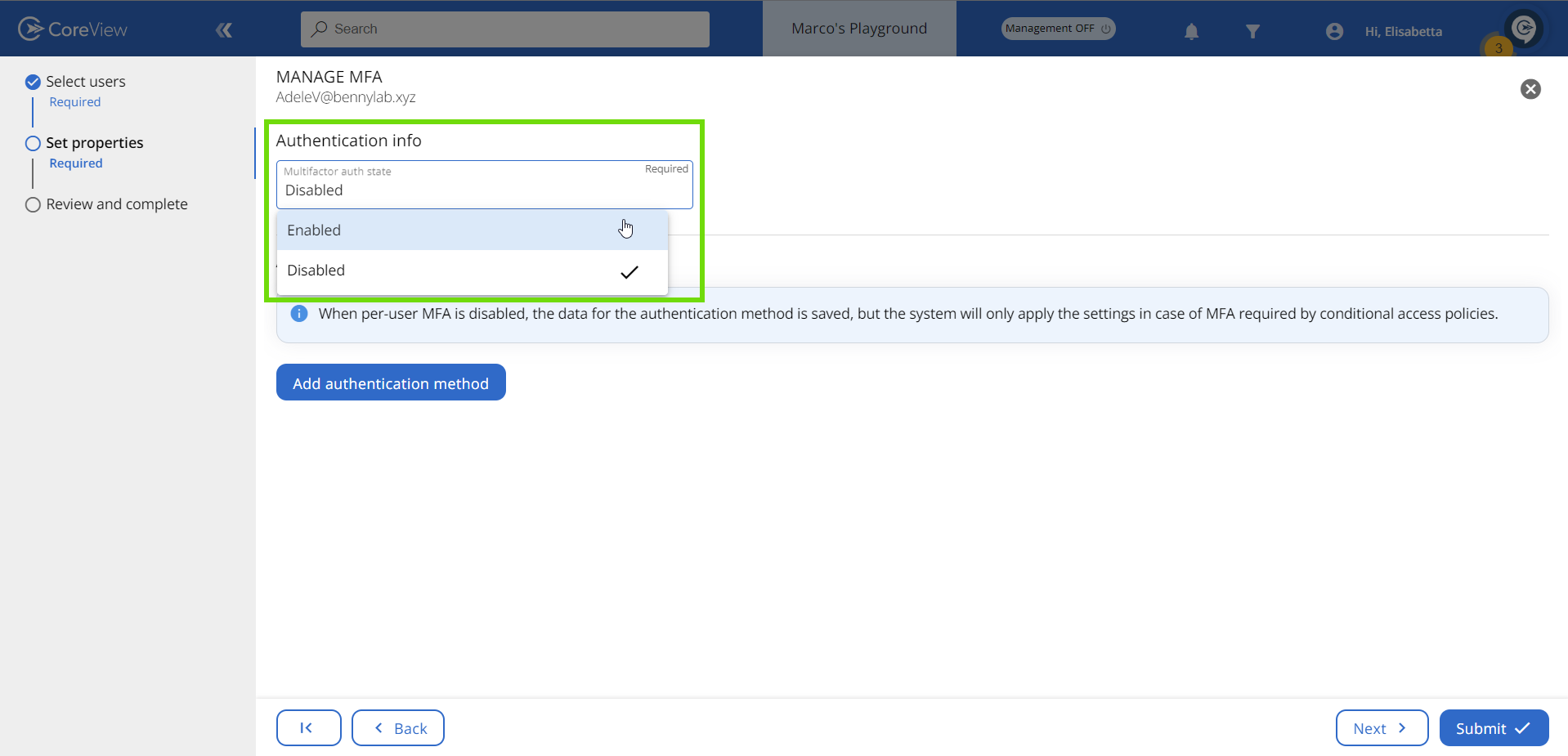
- Click on the “Submit” button to execute the management action.
It's important to note that enabling MFA for a user doesn't automatically enforce MFA. It will only be activated once the user completes the MFA process during their next sign-in to the Microsoft 365 webpage or app.
What’s the difference between MFA “Enabled” and “Enforced”?
Microsoft Entra uses various terms to display the multi-factor authentication (MFA) status for each user. These user status indicators are shown in the Entra ID portal and are turned off by default.
There are three different MFA states:
- Enabled: the user has been enrolled in MFA but has not completed the registration process. They will be prompted to complete the registration process the next time they sign in.
- Enforced: the user has been enrolled and has completed the MFA registration process. Users transition from the “Enabled” to “Enforced” state automatically once they register for Entra ID MFA.
- Disabled: this is the default state for a new user who has not been enrolled in MFA.
Please note, in the context of enforced MFA user status, certain older non-browser applications, such as Office 2010 or earlier versions, may not support modern authentication protocols. To facilitate MFA for user accounts within these applications, while Entra ID multi-factor authentication remains active, app passwords can serve as an alternative to the user's regular credentials.
To check whether per-user MFA has been enabled through CoreView, refer to the “How to check the MFA status of a user” article.
Confusion scenario
Sometimes, you might see a situation where “Enabled” and “Enforced” states seem to act the same. This means the user has MFA turned on and can use it, but their state still shows as “Enabled” instead of “Enforced”.
Explanation
This can happen if you turn off MFA for users after they've finished the registration process, and then turn MFA back on. The registered authentication method is still there, but the user didn't go through the MFA registration process again.
To change the user status to “Enforced”, you have two options:
- An admin can forcefully change the status to “Enforced” from the portal.
- You can ask the user to register their authentication methods again from the portal.

